

“If you click that link, your computer will combust, your bank will empty, and alien warships will descend to claim your soul.”
Dramatic? Absolutely. Effective? Hardly. Fear-based messaging about cybersecurity threats may grab attention for a moment, but it quickly loses its impact. Why? The human brain shuts down when overwhelmed by fear. This phenomenon, known as “fear fatigue,” leaves people disengaged, scrolling through social media, and no closer to addressing real cybersecurity challenges.
In other words, scare tactics make a memorable impression—but mostly a negative one. They don’t encourage long-term behavioral change, which is what we actually need when facing digital attacks.
After all, cyber-attacks come in many insidious forms—phishing, ransomware, deepfake impersonations—and if people are simply numb to fear, they won’t learn to counter them effectively. To truly prepare individuals for digital threats, we need to shift the narrative from fear to confidence and from panic to practical action.
To build truly effective, psychologically savvy security awareness content, you’ve got to know a few fundamental truths about the human mind.
Fear Fatigue—And Why It FailsAccording to reams of psychological studies, people have limited capacity to remain on high alert. When we bombard employees or users with constant doomsday warnings, the initial spike of panic quickly crashes into apathy.
As soon as fear hits a certain threshold, the average human’s response is to escape or deny the threat. The result? You do not get the vigilant, engaged posture that every Chief Information Security Officer dreams of. Instead, you get a workforce that shrugs and says, “Eh, all hackers are unstoppable anyway. Why bother?” That attitude, my friend, is a surefire recipe for cybersecurity threats to flourish.
Self-Efficacy as the Gold StandardPsychologist Albert Bandura introduced the concept of self-efficacy, which is basically the belief that you can perform the actions needed to manage a situation. When applied to security awareness, people who believe they can protect themselves from digital attacks are far more likely to adopt—and stick to—safe behaviors.
So that’s your job in security training: instill that sense of “I can do this.” Instead of relentlessly pointing out the dire consequences of a slip-up, show them the steps, tools, and skills needed to keep the wolves at bay. Then, watch them become your strongest line of defense.
Positive Psychology in Security AwarenessNow we come to the heart of the matter. Cue the warm lighting and uplifting music because positive psychology is our hero. And let me just say, it’s probably more hero material than a fear-based approach which, let’s be honest, can get a tad Melodramatic Reaper at times.
Positive psychology focuses on harnessing strengths, fostering resilience, and empowering individuals. Sound like something you’d want in your training program? Precisely.
Martin Seligman’s PERMA model is typically used to promote well-being, but it’s equally potent for cultivating a security-savvy culture.
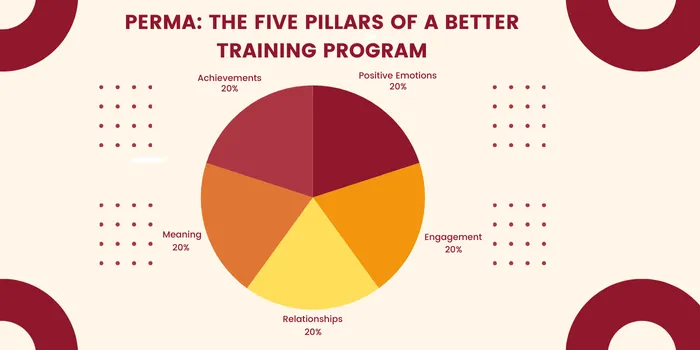
PERMA stands for:
Let’s break it down in a cybersecurity context:
While psychology and positive reinforcement are key components of effective security awareness, technical fundamentals remain indispensable. Firewalls, encryption, and zero trust architecture are critical elements of any robust security strategy—and we’ll address those in detail.
However, no security framework is complete without a strong foundation of guiding principles. These principles not only support technical defenses but also account for the human element, bridging the gap between systems and behavior.

As organizations face evolving cybersecurity threats and cybersecurity challenges, it’s essential to integrate both technical and psychological strategies to build a truly resilient security posture. Let’s explore the foundational principles that bring it all together.
Defense in DepthDefense in Depth is the old faithful of security architecture. The point is to have multiple layers so a single breach doesn’t bring the whole operation down. It can include the following:
None of these alone is a silver bullet—but combined, they reduce the overall risk of cyber attacks.
Least PrivilegeLeast Privilege ensures that every user gets the bare minimum rights necessary to do their job. This cuts down on “privilege creep,” where folks accumulate more access over time than they actually need—leading to massive vulnerabilities. Regular recertification helps maintain the status quo, checking if someone still requires those privileges or if they’re hoarding keys to the kingdom like a digital Gollum.
Separation of DutiesSpeaking of not letting one person run amok: Separation of Duties means critical tasks require more than one individual’s approval or oversight. Think: no single person can approve a $5 million wire transfer and hit send. This forces collusion for malicious activity to happen—and criminals aren’t typically the best at forming long-lasting partnerships under secrecy.
Secure by DesignSecure by Design says from the earliest planning phase—requirements, design, coding—you incorporate security considerations. If your system or your new custom software is built with security at its core, you’re less likely to scramble to patch holes later when you find out your microservice is basically a digital attacks magnet.
Keep It Simple, Stupid (KISS)Complexity can be the nemesis of security. The more complicated your password policies, the more likely someone’s going to have 20 sticky notes around their monitor or reuse a single password across all the logins.
KISS. If you make security easy, people will actually do it. If you make it painfully convoluted, they’ll do the “uh-huh, sure” nod while quietly disabling your precious host-based intrusion detection system the first chance they get.
Security by Obscurity—Don’t Do ItNever rely solely on “nobody knows about it, so it must be safe.” Legendary cryptographic principle: if your entire system’s security depends on the algorithm being secret, you’re in trouble.
Because eventually, that cat will come out of the bag—and your fortress built on illusions will come crashing down. Put your faith in well-reviewed, properly tested algorithms that rely only on the secrecy of keys, not the secrecy of the design.
Remember that corporate training video where the host, stiff as a board, told you to never click suspicious links, and you dozed off? That’s the problem. People do not respond well to monotony, especially regarding something as intangible as cybersecurity platforms and policies. So let’s shift gears and talk about how to rope them in with sugar rather than vinegar.
Rely on Intrinsic MotivationHumans do things long-term when we believe in them. That’s why bribing someone with a $5 Starbucks gift card to watch a 60-minute security training might get you completion numbers—but not real buy-in.
Instead, show employees:
When you tie cybersecurity awareness to personal safety and well-being, you stoke that little flicker in the brain that says, “This matters to me, not just my boss.”
The Role of Humor and RelatabilityHumor helps break down defenses. A witty campaign can stay in your mind far longer than a solemn slideshow. Why do you think comedic commercials are so effective?
If we give employees a silly skit demonstrating phishing, or a comedic role-play featuring a cartoonish “Hacker Bob,” they’ll remember the scenario. They’ll also be more likely to recall the serious message behind it: “Never open attachments from suspicious senders. And definitely don’t respond to a ‘Nigerian Prince’ when your coworker’s name is obviously not Prince.”
Now, let’s not forget the intriguing world of technology solutions that can help us defend against digital attacks. Even in this realm, we can’t rely entirely on the tools—human vigilance is always required. But, oh, we can sure make life easier by implementing the right gadgets and gizmos.
The Rise of AI-Driven Phishing & DeepfakesPicture a cunning adversary forging a perfect clone of your CFO’s voice or face. This is not sci-fi—it’s happening now, courtesy of powerful AI. Deepfakes have already caused multi-million-dollar losses. Cybersecurity challenges intensify as criminals craft unbelievably realistic phishing or voice calls instructing employees to send money.
Meanwhile, generative AI can produce near-flawless phishing emails and sans grammar mistakes. We used to spot suspicious emails because the grammar was so… abysmal. Not anymore. This is exactly why your fear tactics no longer suffice. The attack is subtle and sophisticated. People need empowerment, knowledge, and a bit of wariness to handle it.
Passkeys Over PasswordsThe grand old password might be (finally) dying. We’re stepping into an era of passkeys—secure credentials aligned with the FIDO (Fast Identity Online) Alliance specs. So if your cybersecurity program hasn’t flirted with passkeys yet, you might be missing out.
According to recently published data, passkey usage soared in the last year (4.2 million passkeys stored in one password management platform alone). This is because passkeys are simpler for users (KISS principle) and more robust in the face of typical cybersecurity threats.
You’ve launched a creative and engaging security awareness campaign. Employees responded positively—they laughed, participated, and even appreciated the posters featuring the charming “Encrypted Eddie.” But here’s the key question: how do you measure its effectiveness?
In the face of cybersecurity threats and cybersecurity challenges, a successful campaign isn’t just about engagement—it’s about results. Let’s explore how to evaluate whether your efforts are truly driving meaningful behavioral change.
Behavior-Based MetricsTraining completion rates are a start, but they don’t tell you if Linda from HR will actually smell a rat when a suspicious “invoice” lands in her inbox. Instead, measure changes in user behavior:
Data from these indicators reveals real transformation. If we only rely on “everyone passed the quiz,” we might be missing the fact that half of them cheated or blindly answered “C” to everything.
Continuous ReinforcementChanging human behavior isn’t a one-and-done affair. Think about new year’s resolutions—how many times have they fizzled out by February? We need continuous reinforcement, especially regarding cybersecurity platforms that update regularly, new forms of cyber attacks, and fresh compliance requirements.
Regular, bite-sized trainings throughout the year help employees stay awake, engaged, and maybe even a bit excited if we keep it creative. Add frequent reminders in newsletters, social channels, or Slack. Reward good behavior—like praising someone who identifies a phishing attempt. That positive feedback loop makes them more likely to do it again.
Here we stand, dear friend, at the edge of a new dawn for security awareness content. No more cheap jump-scare tactics or sermonizing. Instead, we’re venturing into territory that acknowledges human psychology, fosters empowerment, and leverages humor and positivity to instill real, lasting changes in behavior.
You can rest assured that it’s not just about coaxing your staff into paying attention to training modules. It’s about weaving security into your organization's very culture: from how your IT teams set up systems with security by design to how your leadership fosters a blame-free environment where employees feel comfortable asking questions and reporting suspicious activity.
The synergy of humans and technology is exactly how we battle—and hopefully outsmart—cybersecurity threats.
Oh, and one last gentle reminder: If you’re about to click that link from a “Prince” who just wants your bank details, maybe pause. Instead, calmly forward it to your security team, wait for them to confirm it’s malicious, and collect your well-deserved “Security Hero of the Month” mug.
Because that’s where we want to be: a place where we celebrate small victories, build each other’s self-efficacy, and collectively shrug off the gloom of fear tactics.
At LexiConn, we specialize in crafting psychology-driven, technically sound content that resonates. From in-depth blogs to thought leadership articles, we help cybersecurity companies connect with their audience.
Discover how behavioral psychology, technical expertise, and compelling narratives can transform your security awareness campaigns into unforgettable experiences.
Book a Free Content Strategy Call Today!
I have read and accept the Privacy Policy
Read More